Hair pulling tools cause safety accidents, and "alternative infrastructure" must be prevented
Original | Odaily Planet Daily
Author | Loopy Lu
Last weekend, a product that seemed to have little connection with the encryption world entered the field of vision of the encryption community. Bitbrowser, which is often used for “multi-opening” and “group control”, has caused large-scale wallet theft, and the amount of damage has reached hundreds of thousands of dollars.
Previously, random number generators, smart contract programming languages, iOS/Android system risks, etc. have all caused large-scale security incidents. As the encryption world matures and becomes more complex, the security situation becomes more and more dangerous, and risks quietly appear in many places that are difficult for people to detect…
What is Bit Browser?
For most encryption users, the name of the product “Bit Browser” may be a bit unfamiliar.
Its full name is “Bit Fingerprint Browser”. According to information on its official website, ** the main function of this product is environment simulation, similar to the “sandbox” function, which can simulate different user tracking information in each window, including IP, device information, browser information, etc. **
This series of functions mainly serves one goal: to simulate multiple users so that each “user” can have independent information. The browser even provides a group control function.
The market audience of Bit Browser is mostly foreign trade e-commerce (such as Amazon, Shopee, etc.) and social media operations (Facebook, Tiktok, etc.). The slogan on its official website states - “Easily manage your large cross-border business with a Bit Browser.”
![Security accidents caused by hair brushing tools, “alternative infrastructure” must be guarded against] (https://img-cdn.gateio.im/resized-social/moments-7f230462a9-874d5ae67a-dd1a6f-1c6801)
Although this product is not specifically designed for users in the crypto world, its series of functions exactly meet the needs of woolists. Therefore, a large number of “hair brushers” have used this product.
There are different opinions on the reasons for the theft.
Recently, a group of members of the “Luomao” community discovered that their Lumao wallets had been stolen. After self-examination, the victims all believed that the theft was caused by the use of a bit fingerprint browser, and the direct cause was the leakage of the private key.
The BitFingerprint browser official responded immediately in the community: some versions of WPS For Windows have a remote code execution vulnerability, and attackers can use this vulnerability to execute arbitrary code on the victim’s target host, control the host, etc. (What does WPS have to do with Bitbrowser users? Bitbrowser’s explanation is that because this vulnerability is easier to trigger, it may be hacked after clicking an unknown link.)
And because the software is far away from the encryption world, it gave a ridiculous response for a while.
![Security accidents caused by hair brushing tools, “alternative infrastructure” must be guarded against] (https://img-cdn.gateio.im/resized-social/moments-7f230462a9-10fb22a4de-dd1a6f-1c6801)
The initial response was widely circulated as a meme in the crypto community.
Bit Browser’s explanation undoubtedly failed to convince users. On August 26, Bit Browser followed up on this incident and issued an announcement saying, “The server cache data has been hacked. User wallets that have turned on the “Extended Data Synchronization” function are at risk of being stolen. It is recommended to transfer wallets assets.”
Security incident, whose fault?
At the beginning of the incident, there were different opinions as to the reason for the theft.
In the MetaMask plug-in we often use, the private key is not saved in plain text. Therefore, hackers only rely on the user’s local cache data and cannot gain control of the user’s assets.
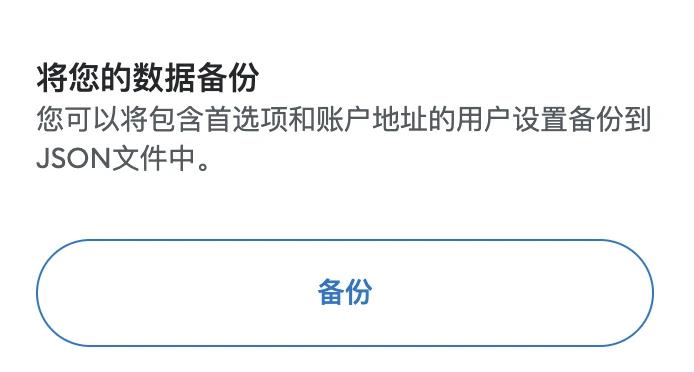
In wallet transfer, besides the most common “export” function, the “backup” function is a function that is less used by people.
MetaMask’s “Backup” feature
It should be noted that the “backup” function provided by MetaMask is completely different from exporting private keys/mnemonic phrases. After backup, the user can obtain a json file, which is also called keystore. *(Odaily Planet Daily Note: A simpler explanation is: private key = mnemonic = wallet control = keystore + password) *
The same is true for locally cached data, so how was the user’s wallet stolen?
After two days of analysis by all parties, the cause of the case was finally identified. The hacker obtained the user’s extended cache by invading the server. **(Odaily Planet Daily Note: In this way, the hacker has the local data of the wallet, but cannot log in.) **Then, the hacker violently cracks the wallet password by “trying common URL platform password collision”, and then obtains the wallet permissions.
Server records show that the server storing the extended cache has traces of being downloaded in early August (log records are as late as August 2), and has locked several IPs, all of which are overseas addresses except for one Jiangsu address. According to people in the community, the case has now been accepted by the Changping Branch of the Beijing Public Security Bureau.
**When we reviewed this incident, we found that it was difficult to clarify the responsibilities of all parties in this incident. **
The first is the first risk point: cache data leakage.
Some users questioned why the cached data was not encrypted? Bit Browser pointed out that when synchronizing “extended data”, the data transmission is encrypted. However, if the software but the main program EXE file is cracked by a hacker, the hacker may obtain the extended data.
However, relying solely on cached data cannot obtain user assets. Only the combination of “cache data + password” can control the wallet. In the daily use of users, it is normal for multiple accounts to share passwords. The passwords of our commonly used Web2 websites are also often leaked. Hackers may obtain the passwords of other Web2 websites and try to “stuff credentials” on the user’s Web3 wallet.
In addition, brute force cracking is also a possibility. Because the number of potential combinations of unlocking passwords is much smaller than the combination of private keys, it is entirely feasible to brute force the unlocking password. (Assuming the product does not introduce precautions such as max failed attempts lockout.)
From the user’s perspective, Bit Browser takes away the cached data of the plug-in and eventually causes the leak. It is true that it has an unshirkable responsibility. However, the failure of wallet access password protection also comes from the long-term deterioration of the network security environment.
Alternative Infrastructure
For software developers, we don’t know why the name “Bit” of “Bit Fingerprint Browser” comes from, but one thing is clear, this product is not created for the encryption world, just to meet Cryptographic user needs.
The more complex a system is, the more potential risk points there are. Any single point of failure may bring the risk of being invaded.
Recalling the wild days of encryption, people only used the most basic Bitcoin wallets. At that time, there were no interactive links such as DeFi and cross-chain. As long as you keep your private key, it’s safe enough.
But now, various off-chain auxiliary tools and on-chain capital pools have added additional risks. More and more products like Bitbrowser are becoming a new alternative “infrastructure” in the encryption world. A large number of “non-encryption” security vulnerabilities endanger the encryption world:
- On August 21, hackers stole 3.13 million USDT. Security personnel believe that the stolen Android system photo album was compromised and the hacker obtained a screenshot of the user’s private key.
- In early August, a huge theft occurred at Curve. Analysis at the time found that there was no problem with the security of the Curve contract, and the reason for the theft came from a vulnerability in its programming language vyper. Therefore aleth, peth, mseth, crveth pools are utilized.
- In May, the synchronization function of Apple ID also caused the theft of more than 10 million US dollars. Many users will purchase or use other people’s US Apple IDs. The account owner can synchronize the local data of the wallet, and only need to break through the wallet access password to gain control of the wallet. This is exactly the same as the Bit Browser theft incident. The total amount of stolen funds from victim users exceeds 10 million US dollars.
- On the developer side, the security situation is more complex. In last year’s Solana wallet theft case, the risk point came from the random code related to the lower-level mnemonic phrase generation.
With the complexity of the encrypted world, more and more tools, software, and services that are difficult for people to detect may be included in the encrypted world in the future, and the risks will also expand.
Odaily Planet Daily would like to remind you not to hand over the local data of your wallet to others or over-authorize it. In addition, due to the hidden nature of the risk, please be cautious in using electronic means to save private keys/mnemonic phrases. Do not install too many unknown software on computers that frequently perform encryption operations.
Related Reading
“Hacker incidents occur frequently, please accept this Crypto anti-theft guide”